Featured Posts

April 23, 2024
Understanding QTSP
Read More
April 22, 2024
Role of PKI in Aviation Security and Compliance
Read More
April 12, 2024
SSL: A Guide for Government Institutions
Read More
April 11, 2024
How Managed PKI Solutions Enhance Data Protection in Government Agencies
Read More
April 10, 2024
Streamlining Government Processes with emSigner
Read More
April 08, 2024
Understanding the Role of PKI Services in Manufacturing Security
Read More
April 03, 2024
IAM Solutions for Efficient Identity Management in Telecom Systems
Read More
April 02, 2024
Understanding the Role of PKI Services in Government Security
Read More
April 01, 2024
Role of Digital Trust in Sustainable Business Practices
Read More
March 29, 2024
Digital Identity in the Travel Industry: Enhancing Customer Experience
Read More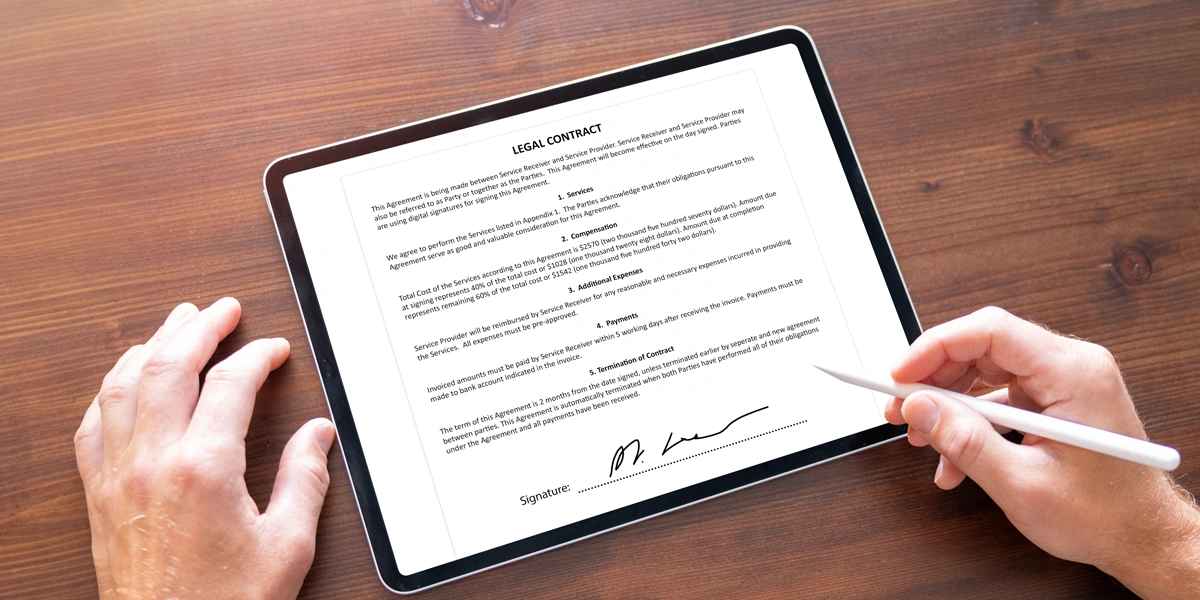
March 28, 2024
eSignature Security: Safeguarding Digital Transactions
Read More
March 27, 2024
Role of Biometrics in Enhancing Digital Identity Verification
Read More
March 26, 2024
Future of Digital Trust: Predictions and Trends
Read More
March 25, 2024
Government Services Transformed: The Digital Trust Effect
Read More
March 22, 2024